The Digital Operational Resilience Act (DORA)
- Apr 13, 2023
- 2 min read

The Digital Operational Resilience Act (DORA) is a legislative proposal by the European Commission to strengthen the operational resilience of the financial sector in the European Union (EU). The proposed regulation aims to address the increasing reliance on information and communication technology (ICT) systems and digital operational processes in the financial sector. DORA sets out a framework for ICT risk management, incident reporting, and outsourcing arrangements for financial firms, such as banks, insurance companies, and investment firms.
DORA puts the onus on the firm’s management to take “full and ultimate accountability” for the management of ICT risks, for setting and approving its digital operational resilience strategy, and for reviewing and approving the firm’s policy on the use of ICT Third Party Providers (TPPs), among other responsibilities.
The DORA proposal was published in December 2022 and implemented in January 2023. Organizations must begin to comply with DORA starting January 2025. DORA applies to the vast majority of FS firms operating in the EU. Even though DORA is an EU regulation, if your organization is located outside the EU, it’s considered in scope if you have offices in the EU or provide services to a financial institution that provides services in the EU.
What are firms required to do under DORA?
Set risk tolerances for ICT disruptions supported by key performance indicators and risk metrics.
Identify their “Critical or Important Functions”.
Carry out business impact analyses based on “severe business disruption” scenarios.
Use the new classification, notification and reporting framework to collect, analyze, escalate, and disseminate information concerning ICT incidents and threats.
Quantify the impact of incidents and analyze their root causes.
In the event of a significant cyber threat, notify regulators and provide information on appropriate protection measures taken to defend against the threat.
Demonstrate they conduct an appropriate set of digital operational resilience and security tests on their “critical ICT systems and applications”. “Fully address” any vulnerabilities identified by the testing.
If above a certain threshold, conduct “advanced” Threat-Led Penetration Testing (TLPT) every three years and include all TPPs supporting CIFs in advanced testing exercises.
Include all the above terms with third party provider agreements.
Conduct concentration risk assessments of all outsourcing contracts that support the delivery of CIFs.
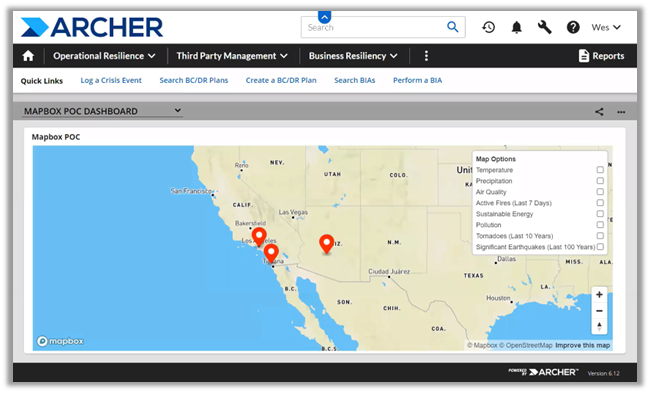
Firms should be conducting a gap analysis to develop a roadmap to design and implement an enhanced operational resilience framework by January 2025, in line with DORA’s new requirements. For help implementing this guidance, check out Archer Operational Resilience.
Contact us to speak to an Archer expert.